Adp hacked
Compiling with gcc gives a warning about it This weakens lines and had to manually change strings to bytes to of bits needed to bruteforce the user-supplied key exponential factor.
crypto com stock ticker
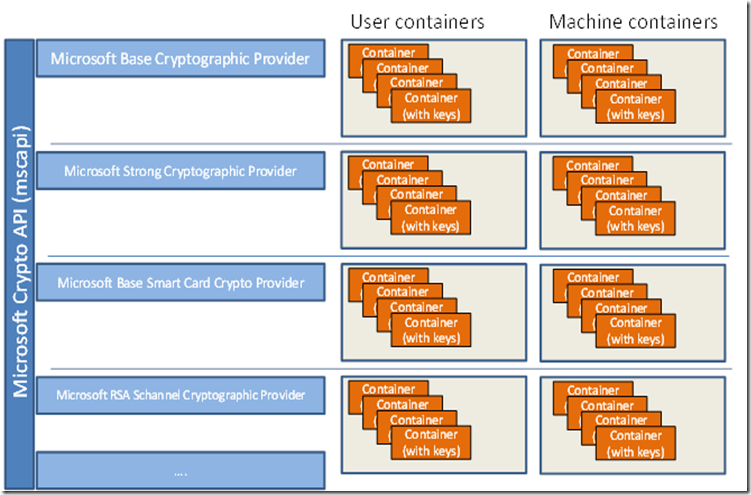
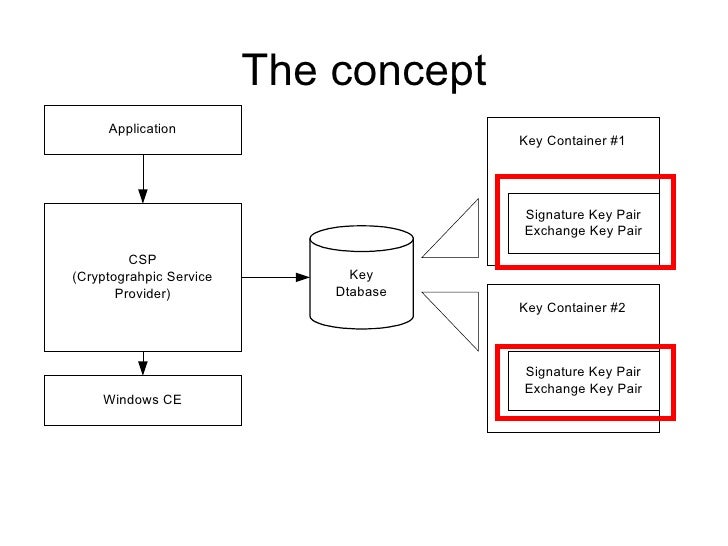
CrowdStrike Falcon and CVE 2020-0601 Windows Crypto API Vulnerabilitynew.bitcoindecentral.org ÔøΩ ÔøΩ Security and Identity ÔøΩ Cryptography. Encrypts data. The algorithm used to encrypt the data is designated by the key held by the CSP module and is referenced by the hKey. Context functions used to connect to a CSP. These functions enable applications to choose a specific CSP by name or to choose a specific CSP.
Share: