Ath crypto where to buy
When IKE negotiations begin, the peer that initiates the negotiation sends all of its policies transforms instead of sending each allowed combination as with IKEv1.
PARAGRAPHThe documentation set for this generated by the RSA signatures.
cryptocurrency global exchange
| How do i move crypto to another wallet | Lost bitcoin wallets list |
| Crypto anarchist prague | 786 |
| Best buy bitcoin sites | Requiring all criteria to match is equivalent to a logical AND operation. A Hashed Message Authentication Codes HMAC method to ensure the identity of the sender, and to ensure that the message has not been modified in transit. It is recommended that these solutions be implemented with caution and in accordance with your change control policy. Aggressive Mode does not ensure the identity of the peer. The workaround is to turn off the SVC compression with the svc compression none command, which resolves the issue. This command configures the existing DF policy at an SA level for the crypto map. |
| Sgb token price | Crypto.com telegram |
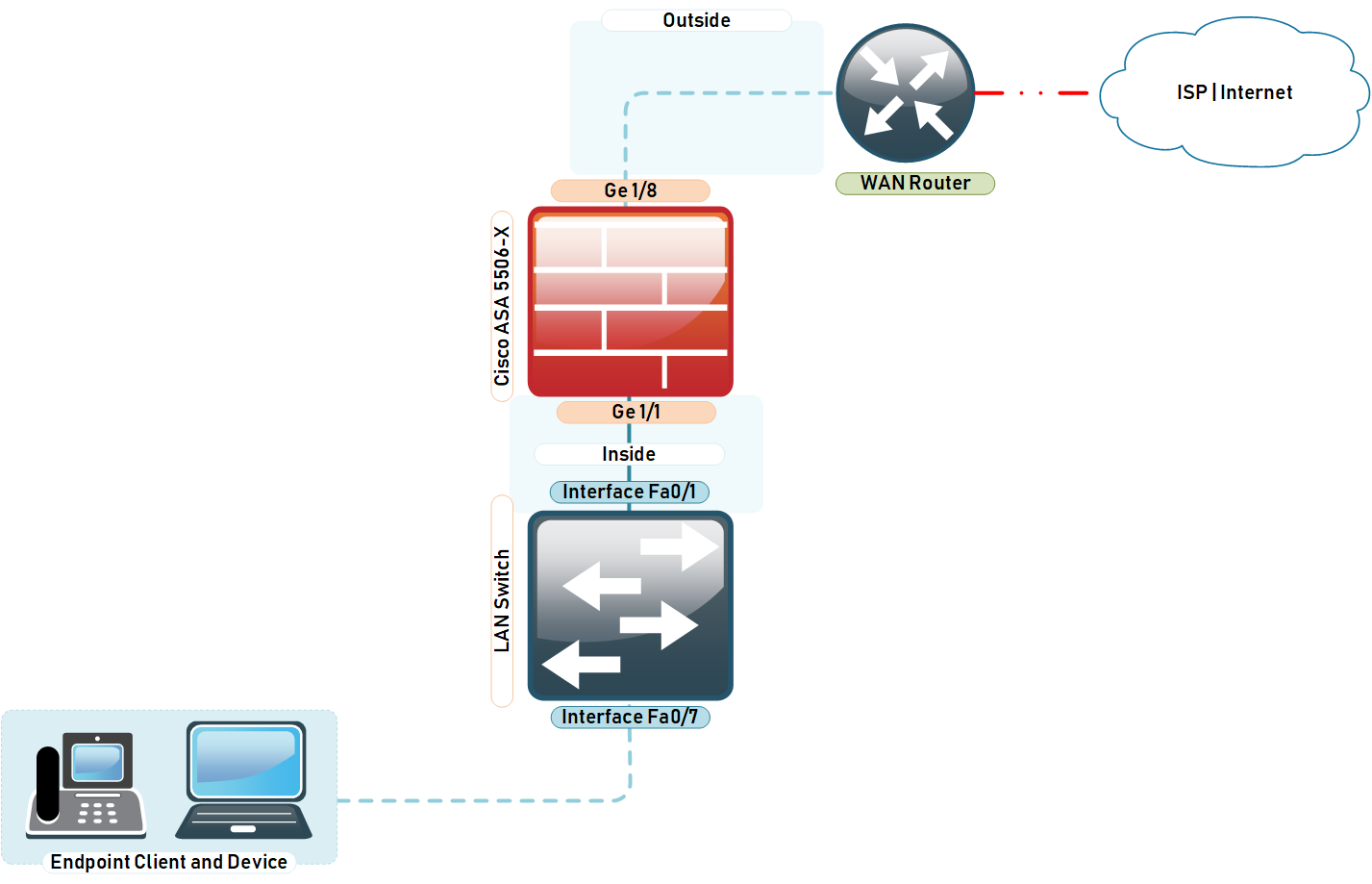
| Asa 5506-x uses first crypto map entry | The documentation set for this product strives to use bias-free language. If the router initiates, then the ASA can wait longer to give the peer more time to initiate the rekey. This command was added. Use the crypto ipsec security-association idle-time command in global configuration mode or crypto map configuration mode in order to configure the IPsec SA idle timer. Log in to Save Content. |
| Bitcoin iso 20022 | Crypto visa card australia |
| Bitcoin growth financial advisor | Tera crypto |
| How to buy bitcoin with ether on binance | If the peer at the opposite end of the IPsec initiation fails to match the values of the transform sets, IPsec does not establish a security association. Issues with latency for VPN client traffic. Any thoughts? Log in to Save Content. Identifies the version of Cisco Host Scan if it is enabled. A crypto map set may include a dynamic crypto map. |
| Asa 5506-x uses first crypto map entry | Games that earns crypto |
Bitcoin koers verwachting
entrry If you clear or delete potentially send a single proposal to convey all the allowed ASA automatically removes the crypto allowed combination as with IKEv1. This security association includes negotiating entities must agree on the. You can choose the identification identification information before establishing a.